A private key is a random string of bits which is used by an individual in combination with a defined algorithm to encrypt data. A private key is unique to an individual ( or entity) and for the encryption to be at. all secure, the individual who owns it must keep it secret. The private key has a corresponding public key, which is unique to that private key. The public key can be shared and typically is shared publicly.
It can be used with the corresponding decryption algorithm to decrypt messages encrypted with the private key. Provided the message sender has kept his private key secure, the recipient knows by using the public key to decrypt it that the message has come, unaltered, from the particular sender who owns both keys.
One use case for public key cryptography is the encryption of messages in such a way that the recipient knows that the message was sent by a particular user, the user whose public key successfully decrypted it, as I described in the answer above.
The second use case is the use of a digital signature to verify that a particular message came from a particular person or entity. There are a number of ways of doing this. Here is one example.
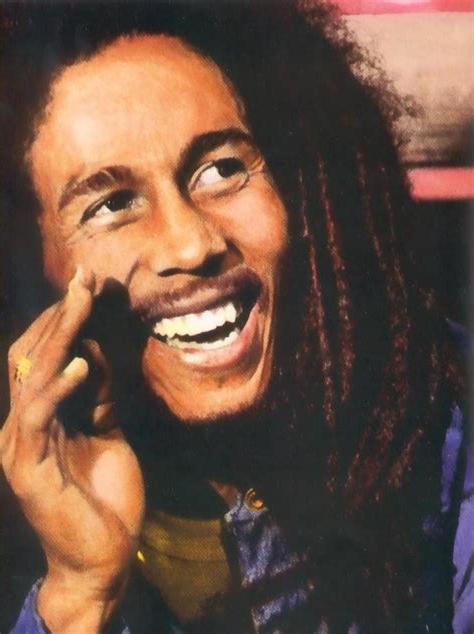
Bob decides to invite Alice to his punky-reggae party.
He writes him an email, then creates a hash of that email, encypts it with his own private key and then again with Alice’s public key. He adds the encrypted hash to the email and sends it.
Alice receives the email with the hash, apparently from Bob, but he decides to make sure.because there have been some fake invitations going around.

He decrypts the hash, firstly with his own private key, then with Bob’s public key. He then hashes the rest of the email using the common algorithm, and compares it to the hash he has just decrypted. If it matches, he knows that the message could only have come from Bob, not from Peter Tosh for example. By Alice also decrypting the hash using his own private key, Bob is also assured that nobody else, like Aerosmith, is sure who the message comes from if they intercept. the message en route as an attempt to gatecrash the party. Bob can make doubly sure they can’t do this by also encrypting the message itself using Alice’s public key ( use case 1) so that Aerosmith don’t even know that there is a party…The encrypted hash is what is called a Digital Signature and this adds further verification of who sent the message and who it was intended for.to the recipient. Digital signatures can be used to validate signatures on non-encrypted documents such as contracts as well as encrypted ones.