Here you can ask questions related to this specific course section.
With Solidity 0.8.0, Overflow and Underflow is built in by default now. I read that Safemath is no longer needed to be imported into contracts, and that SafeMath by OpenZeppelin would be deprecated soon.
Are there other SafeMath safety checks that are still valid and so should still be using in our contracts, or does the new Sol version include everything from SafeMath and we shouldn’t add it to our contracts in order to save Gas costs?
Hope that made sense, lol
Ben
Solidity version 0.8 inherit all SafeMath methods, so all contracts from now on dont have to use the SafeMath library anymore, all contracts on a version below 0.8 still need the library.
https://docs.soliditylang.org/en/latest/080-breaking-changes.html
Carlos Z
Hi, I have a question, why does this always appear in my remix and does not appear during the class recordings of Filip? It does not allow me to deploy the contract
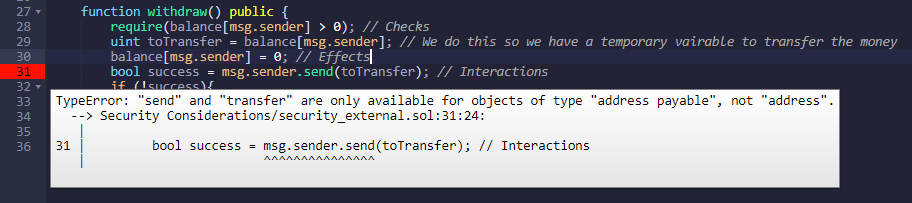
You have to cast msg.sender to payable as shown in the error you posted.
payable(msg.sender).transfer()
You can find these answers also by reading the docs.
Cheers,
Dani
Thank you! This solved a lot of my problems.
I placed payable on the function header before, no wonder it didn’t work. Thanks again @dan-i
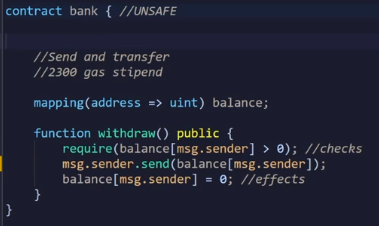
With this code here, when the attack contract calls the withdraw function, is the msg.sender the address of the person that deployed the attack contract or the bank contract.
Could someone possibly explain the process of how the interaction between these two contracts would work because I’m finding it quite confusing.
Thank you in advance
Would you please provide the sample of the attack contract? Which account would deploy the attack contract. How it is interfaced with the bank contract? Can you show also show how the receive() and fallback is called?
I am still confused with the message from this section. Thank you for your help.
Hi @yoeby
is the msg.sender the address of the person that deployed the attack contract or the bank contract.
Can you elaborate what your mean here?
In your function withdraw you are checking if msg.sender had enough balance.
Keep in mind that msg.sender can be either a contract address or a physical person address.
Regards,
Dani
Hi @Paul_Kwok
You have a great example of this in our security course where re-entrancy is explained and coded by Ivan.
Check it out 
Happy learning,
Dani
How do I know when its a contract address and when its a physical person address?
You won’t know, this is why you have to follow the check/effect/interaction pattern to avoid re-entrancy attacks.
Hello.
I have a question about part 3 (Call, Send & Transfer EIP1884) of this series.
What does Filip mean by “send gas to the receiver”? I thought gas is used for transaction fee that the sender pays to the miner, not the receiver. Is gas different from the Ether (money) that the sender sends to the receiver?
I’m a bit confused here.
When using Call, Send & Transfer a gas stipend is attached to the transaction, therefore the receiver contract can use that gas to perform operations (consider that the receiver contract can have a fallback function that is triggered when it receives ether).
Hi guys,
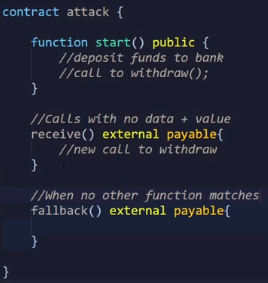
I am trying out different things with the stuff we learn. So for example I tried to use the safe EIP1884 way to withdraw ether and use it in our Bank contract. But the strange thing is that I got an error in a different function (the getBalance function). I can not figure it out by myself how to fix this.
Does someone has a tip? Or is the way I think not the right way?
pragma solidity 0.8.2;
pragma abicoder v2;
import "./Ownable.sol";
contract Bank is Ownable {
mapping(address => uint) balance;
event depositDone(uint amount, address indexed depositedTo);
function deposit() public payable returns (uint) {
balance[msg.sender] += msg.value;
emit depositDone(msg.value, msg.sender);
return balance[msg.sender];
}
function withdraw() public {
require(balance[msg.sender] > 0); //checks
uint toTransfer = balance[msg.sender];
balance[msg.sender] = 0; //effects
(bool succes,) = msg.sender.call{value: toTransfer}("");
if(!success){
balance[msg.sender] = toTransfer
/*function withdraw(uint amount) public onlyOwner returns (uint){
require(balance[msg.sender] >= amount);
payable(msg.sender).transfer(amount);
return balance[msg.sender];
}
*/
function getBalance() public view returns (uint){
return balance[msg.sender];
}
function transfer(address payable recipient, uint amount) public {
require(balance[msg.sender] >= amount, "Balance not sufficient");
require(msg.sender != recipient, "Don't transfer money to yourself");
uint previousSenderBalance = balance[msg.sender];
_transfer(msg.sender, recipient, amount);
assert(balance[msg.sender] == previousSenderBalance - amount);
}
function _transfer(address from, address to, uint amount) private {
balance[from] = balance[from] - amount;
balance[to] = balance[to] + amount;
}
}
I then got this ParserError message in the getBalance function. Weird thing about this is that whenever I use the “non-safe” or original withdraw function that Filip showt us that I don’t get this ParserError.
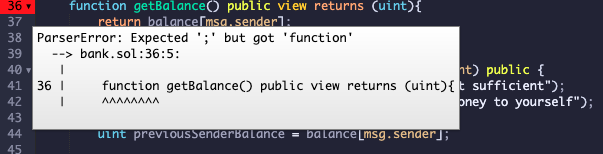
Check if the code lines above that function are missing a ;
Carlos Z
I thought msg.sender is already payable address, so I guess my question is why in this case you have to add payable?
Also another question that I have. What is the difference between those two calls:
msg.sender.call.value(toTransfer)();
vs
msg.sender.call{value: toTransfer}(“”);
I thought msg.sender is already payable address
This changed some months ago with the a new Solidity version.
Also another question that I have. What is the difference between those two calls:
msg.sender.call.value(toTransfer)();
vs
msg.sender.call{value: toTransfer}(“”);
The first one was deprecated, so you should use the new syntax msg.sender.call{value: toTransfer}(“”);
